--[ Anomalía #7 - From 0 to CTF: learning forensics on iOS ]--
May 1, 2026
By: ZoqueLabsThis writing is distributed under a Creative Commons CC BY-SA (Acknowledgment - Share Alike) license.
Spanish version
Hello, hello! Anomaly #7 is here with a little experiment we did to upload sk1llz in iOS forensics.
At Zoque, when we check an iPhone, we usually do the usual: basic extractions (backup and sysdiagnose), run MVT, check some devices manually and, if necessary, rely on allied organizations for a second look.
Even so, we almost always have the feeling that there is “something else” that we could review. iOS still has several blind spots for us. Partly because we have prioritized Android —for regional reasons— and hadn’t invested as much time in strengthening capabilities on iOS.
It was time to change that.
Let’s dust off two resources that we had saved for a long time:
1. Hack.lu 2025 Workshop — Sysdiagnose (link)
In this two-part workshop we learned the basics of saf (Sysdiagnose Analysis Framework), a tool that processes sysdiagnoses and generates structured outputs for analysis. One of its most useful points is the generation of JSONL files, which can be easily integrated with log or timeline analysis tools.
The workshop covers integration with Splunk and how to navigate data by modules and timelines. The second part delves into the internal workings of saf and proposes exercises to build new parsers —, something especially useful, considering the number of artifacts still uncovered.
In the end, the workshop proposes a CTF. That was our second link.
2. iForensics — Hackropole (link)
This CTF (9 challenges, each one more complex than the last) is focused on iOS forensics and is part of the 2025 edition of the Hackropole portal. We recommend following the preparation section, but avoiding seeing solutions: the fun is in solving it without spoilers.
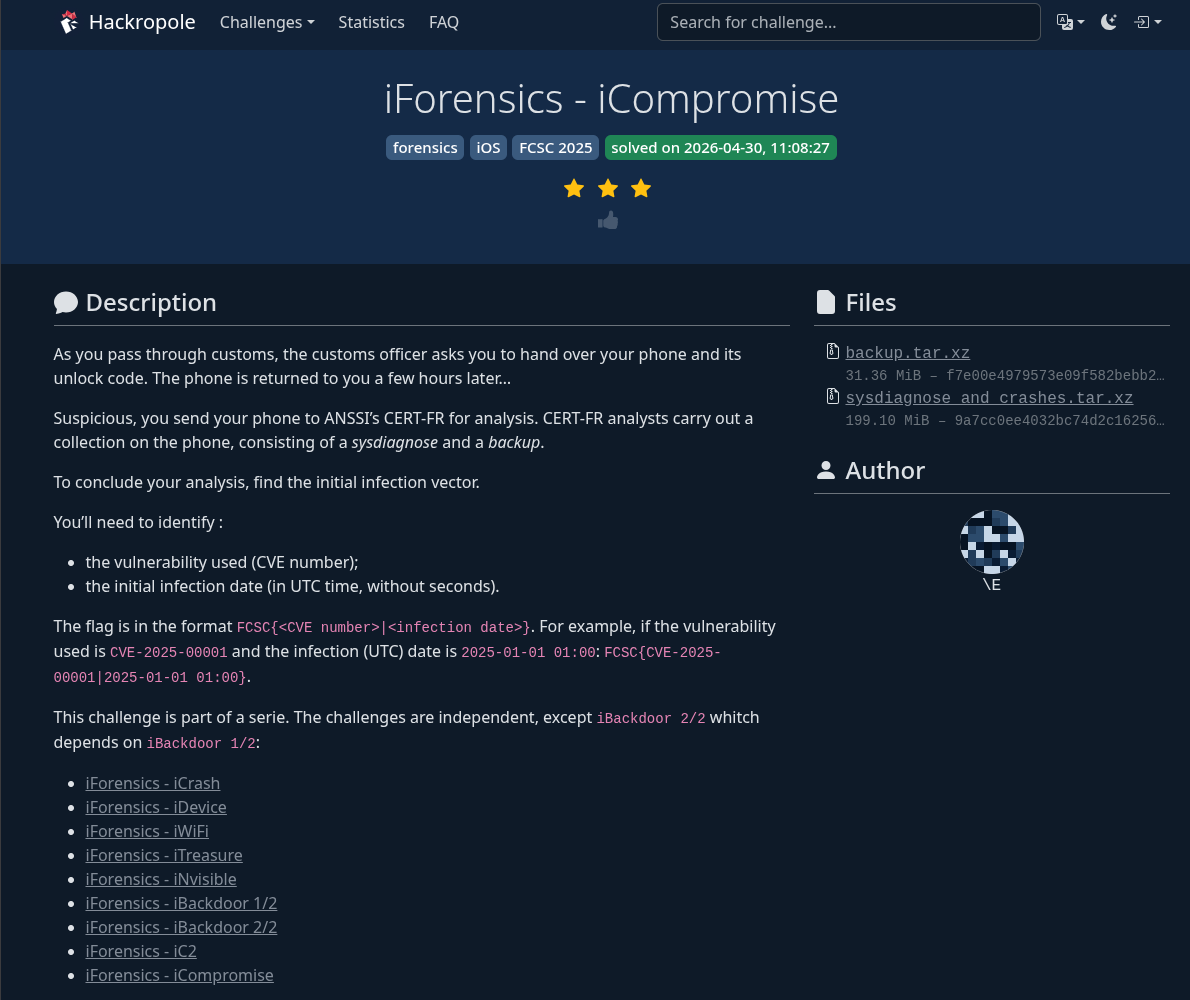 Screenshot of the iCompromise challenge. solved!
Screenshot of the iCompromise challenge. solved!
With saf and Splunk ready, we went in challenge after challenge… and didn’t stop until we finished. We are left wanting more.
We learned a lot and, above all, gained confidence when analyzing iPhone extractions.
We are not going to give clues so as not to damage the experience, but we do leave some useful tips:
- Have a good SQLite reader on hand.
- Know how to read
.plistfiles.
*Try iLEAP for backup analysis (requires old versions of Python; we recommend usinguvto handle environments). - Patience.
Recommended without much thought for anyone who wants to get into iOS forensics.
As always, happy to receive comments or questions at contact [at] zoquelabs.xyz or in our Signal group (you can write to us to add them).
And now, we leave you with the rest of Anomaly, which is loaded.
Happy hacking <3
--[Threat Intelligence ]–
Venezuela - Wiper against the energy sector
Amid geopolitical tensions in the Caribbean, artifacts from a chain of attack targeting the energy sector in Venezuela were identified, uploaded to a public resource in mid-December. The analysis points to a wiper geared towards data destruction —overwriting files and removing system structures— with no extortion component.
Guatemala points towards Venezuela in attribution to cyberattack.
On April 7 of this year, Guatemala’s Arms Control Directorate suffered an attack against one of its platforms, resulting in the leak of approximately 18,000 records (out of a total of 125,000 available). The information displayed includes personal data and details about weapons registered in the name of users, such as models and calibers, which increases the sensitivity of the database. According to official reports, the attack originated from an IP located in Venezuela and the incident was contained before the leak was major.
Mexico and Brazil are the largest originators of connections in DDoS attacks.
A recent Gcore report on the origin and volume of DDoS attacks in the third and fourth quarters of 2025 shows that Mexico and Brazil concentrate about 50% of connections in network layer-based attacks. According to the report, this activity is associated with the massive AISURU botnet and is related to the high number of IoT devices with limited or non-existent security deployed in Latin America.
TGR-STA-1030: Activity in Central and South America
Unit42 records activity of this APT in the region since February. This APT whose origin is unclear has dedicated itself to attacking critical infrastructure for espionage purposes in 37 countries in the last year.
Brazil — botnet-linked anti-DDoS provider against ISPs
An investigation by KrebsOnSecurity describes how a Brazilian company dedicated to mitigating DDoS attacks would have been linked to a botnet used to launch sustained campaigns against other internet providers in the country. The infrastructure, based on compromised IoT devices and Mirai variants, was used to generate large-scale attacks against regional ISPs, in a context where these operators are frequent targets due to their lower defense capacity. The affected company attributes the activity to external intrusion or sabotage, but the case exposes a known pattern: defense infrastructure reused or compromised to operate offensively within the same ecosystem.
--[Surveillance and spyware]–
El Salvador - El Salvador is looking for a replacement for Pegasus
Thenewsground.com reveals information suggesting that the Bukele government continues to actively seek spyware services, despite the Pegasus scandal in El Salvador in 2022, where attacks against journalists and activists were documented. The article exposes part of the network of intermediaries that overshadow the acquisition of this type of tools.
Paragon — silence regarding the investigation in Italy
Amid the scandal over the use of Graphite spyware against journalists and activists in Italy, the company Paragon has not responded to formal requests for information from authorities investigating the attacks. The investigation —opened after alerts from Apple and WhatsApp about infections in 2024— remains unclear about those responsible, while the company had initially offered to collaborate and then cut off communication. The case adds another layer to the commercial spyware ecosystem: tools used against civil society, opaque state contracts and suppliers that can be removed from the process when traceability begins to close.
Predator/Intellexa — exploits purchased on-chain during the Greek scandal
Within the framework of the trial in Greece for the Predatorgate scandal —which since 2022 involves espionage on journalists and politicians and which has already led to convictions against Intellexa executives— key details came to light about how the Predator ecosystem operates: the company It does not necessarily develop the entire exploitation chain, but purchases exploit chain components from external suppliers, including companies in the US. UU., and integrates them into its platform. This allows complete intrusion capabilities (from initial access to device control) to be assembled from distributed parts, accelerating deployments and diluting technical traceability.In the context of the Greek case —with documented use against civil society actors and an ongoing institutional crisis— these revelations show a model closer to an exploit supply chain than to closed spyware development.
Telecom - New research from Citizen Lab: exploitation of SS7/Diameter for tracking
Citizen Lab report describes campaigns that abuse signaling between operators to obtain device location data and manipulate SMS messages. Actors send queries that appear legitimate within the network, relying on interconnection points to integrate into normal traffic. The use of multiple nodes and routes allows the operation to be kept active and makes its detection difficult, which depends on controls and visibility at the signaling level.
--[Malware Technical Analysis ]–
fast16 — Precision sabotage before Stuxnet
SentinelOne’s analysis reconstructs fast16, a sabotage framework dating back to 2005 that already targeted high-precision engineering and simulation software. The implant operated at the system level, intercepting and modifying in-memory calculations to introduce small but systematic errors, difficult to detect and reproducible on multiple machines.
More than direct destruction, the goal was to degrade results: simulations that were apparently correct, but fundamentally incorrect, with potential impact on scientific research and critical infrastructure.
The finding repositions the origin of digital sabotage: before Stuxnet there were already operations designed to manipulate physical processes through software, with a level of stealth and persistence that remains difficult to detect today.
Morpheus / IPS — spyware “low-cost” with full access via deception
The Osservatorio Nessuno investigation exposes Morpheus, an Android spyware attributed to the Italian company IPS that is distributed through fake update applications sent after blocking the target’s connectivity. Once installed, it abuses accessibility services to read screens, interact with apps and scale access, including controlling accounts like WhatsApp through induced biometric verification. The operating model relies on direct user manipulation and the use of telecommunications infrastructure to facilitate installation, with complete low-cost surveillance capabilities.
--[Privacy/Anonymity ]–
Firefox / Tor — fingerprinting via IndexedDB
A Fingerprint analysis reveals a vulnerability in Firefox and Tor Browser that allows a stable identifier to be generated from the internal behavior of IndexedDB, namely the order in which the browser returns stored data. This pattern can be exploited to create a consistent fingerprint between sessions, even in private mode or after rebooting identity in Tor.
--[Leaks ]–
Today with special focus on Guatemala:
Guatemala — exposed university biometric base
One attack compromised data on at least 84,000 studentsand faculty at Rafael Landívar University, including photographs linked to names, dates of birth and academic identifiers. The leaked package (~20 GB) allows visual identity to be correlated with personal data, increasing the risk of spoofing and fraud. The actor “MrGoblinciano” had already been linked to previous incidents in the country’s university sector.
Guatemala — sequence of attacks against the State and universities
April left a chain of incidents that affects multiple layers of the State: leaks on public platforms, data exposure in universities and attacks attributed to different actors (“Gordon Freeman”, “MrGoblinciano”, “NemorisHacking”). Among the cases, more than 200,000 records extracted from government platforms and unauthorized access to systems with missing or outdated basic controls are reported. Institutions, in several cases, deny commitments while reinforcing security measures.
--[ ZOLIM - This week’s snapshot (04/17/2026) ]–
ZOLIM reports 5 new IPs, highlights:
- A new instance of CHAOS Rat in Argentina.
- The infrastructure attributed to Blind Eagle persists on the Colombian coast with DCRat and AsyncRat.
- The presence of Quasar Rat in the region continues to grow with a new instance in Brazil.
- Brazil also registers a new instance of UnamWebPanel.
You can consult all the information and explore by country, IP, city, threat and other filters in the ZOLIM. dashboard